Introduction
Recently, Adobe Photoshop users have been targeted by the Topaz Clean stylization tool installer. There is no other reason than that it installs a plug-in for Photoshop, called Temp Stealer, which is bundled with the installer, and users cannot un-bundle it or even be aware of it.
Combined with posts published on the Dark Web, its author states that Temp Stealer can exfiltrate crypto wallets (over forty types), browsers, and other sensitive information for data breaching and reselling.
According to our observation, Temp Stealer has such strength and it is often bundled with the cracked version of the software. Taking Topaz Clean as an example, Temp Stealer sits in the /temp/ directory when the user clicks this installer. Of course we could remove it, but we will soon discover that the installer has created an auto-run registry entry ready for the Temp Stealer persistence.
Vulnerability
How is the installer bundled? Was it voluntary or purposeful? This still needs to be determined. However, its trajectory shows that the Temp Stealer, a 64-bit GUI (Graphical User Interface) executable compiled in C/C++, is dropped by file hash and connects to an embedded IP 79.137.199.73 after execution.
Then, it checks for the wallets in the system to steal the file related to the corresponding ones. Temp Stealer targets the crypto wallets such as Exodus Web Wallet, BitAppWallet, BinanceChain, and so on, which are hard coded in the Temp Stealer binary.
Following this, the malware steals cookies, usernames, passwords, auto-fills, and history from Chromium and Firefox-based browsers. Now we have restored part of its pseudo-code to search recursively between all installed browsers.
In addition to browsers, Temp Stealer is also interested in Steam and Telegram applications. After thoroughly checking the registry, it sifts out active applications and steals information such as player profiles and passwords from Steam Sentry File or Config file; and session data, messages and images from Telegram tdata or working folder. At the same time, the malicious software takes a screenshot of the current system and saves it for exfiltration.
Temp Stealer wants much more than that. We find it calls a particular URL to get the victim’s geographic location, such as country, city, time zone, and zip code. It also collects details of RAM, Processor, GPU and authorization like Discord token file and FileZilla session file from targeted systems. After getting all the above information, it will send the data to the attacker’s remote server, the same IP connected before.
Remediation
Due to increased digital transactions and crypto-currency usage, malware authors continuously create new stealers. Threat awareness and protection means are indispensable to avoid the risks involved, so we offer a few suggestions for your reference:
- Avoid downloading cracked software from unknown websites
- Use strong passwords and enforce multi-factor authentication whenever possible
- Block URLs that can be used to spread the malware
- Monitor the beacon on the network level to block data exfiltration by malware or TAs (Threat Actor)
- Enable Data Loss Prevention (DLP) solutions on systems
Implementing the Fix
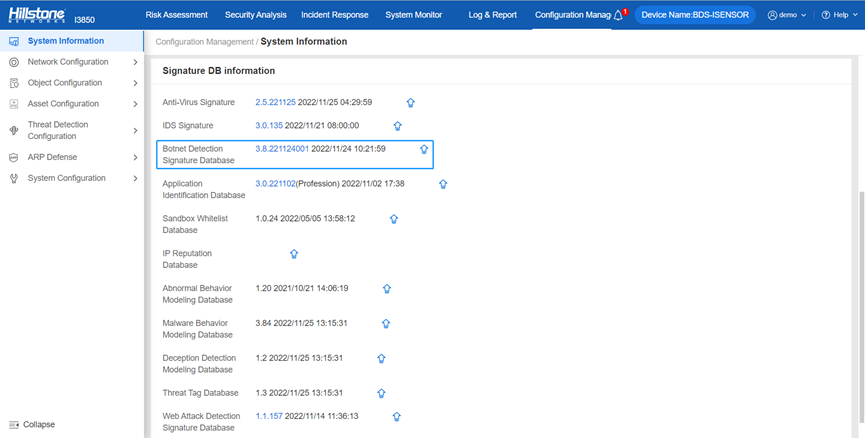
Hillstone botnet detection signature database can provide adequate protection against this vulnerability. Devices such as Hillstone Server Breach Detection System (sBDS), can support this signature via an update to the newest version, 3.8.221124001.