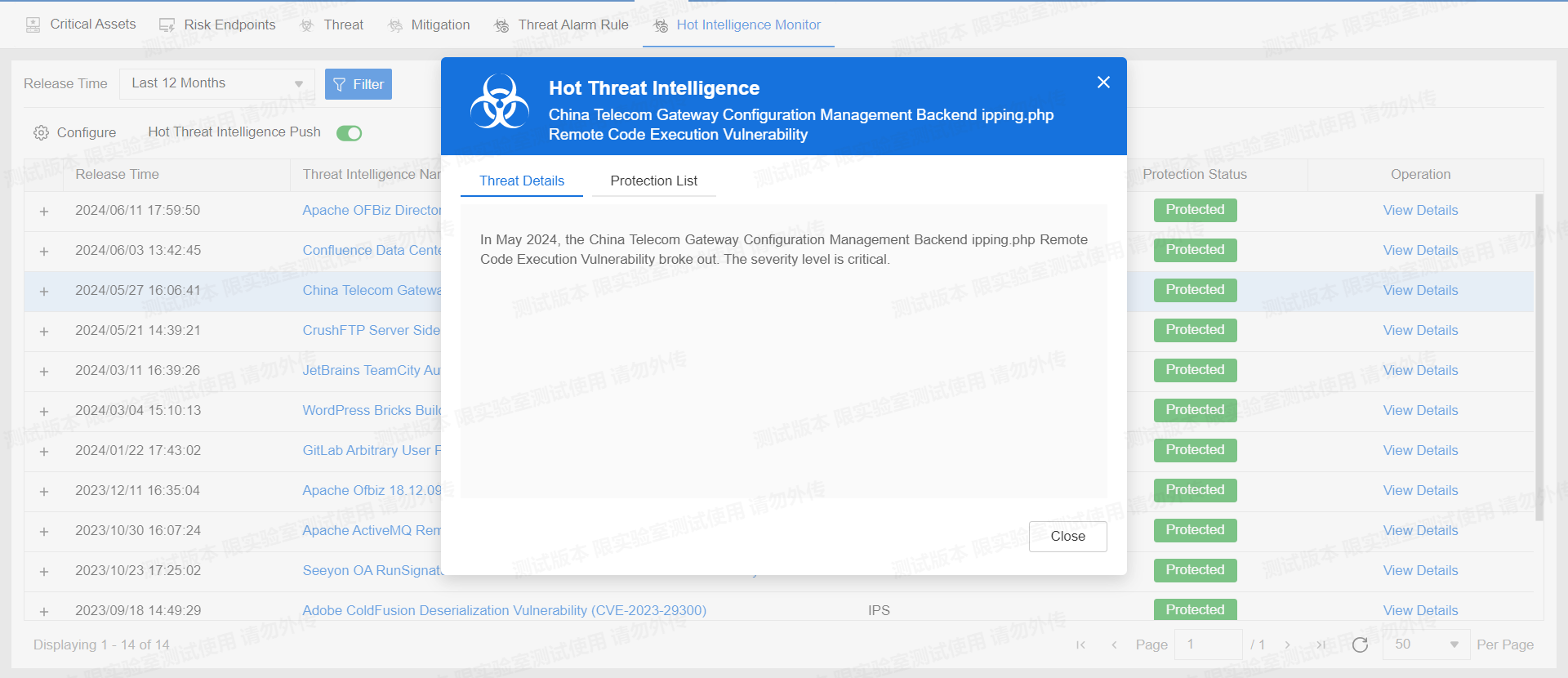
China Telecom Group Limited is a large telecommunications company in China. In May 2024, a critical security vulnerability was discovered in the China Telecom Gateway Configuration Management Backend, which allows malicious actors to execute arbitrary commands on the affected system, potentially leading to severe consequences such as data breaches, system takeovers, and further exploitation of network resources.
Vulnerability
The China Telecom Gateway Configuration Management Backend ipping.php remote code execution vulnerability stems from improper handling of user inputs within the backend management system. An attacker can exploit this vulnerability by sending specially crafted HTTP requests to the ipping.php script.
The key techniques and tactics used in exploiting this vulnerability include:
- Injection of Malicious Commands: The vulnerability allows attackers to inject arbitrary commands through user inputs that are not properly sanitized. This means that if the input fields in the ipping.php script do not adequately filter out dangerous characters or commands, an attacker can insert commands that will be executed by the system.
- Remote Code Execution (RCE): By exploiting the vulnerability, attackers can execute commands remotely on the affected server. Remote code execution is a critical vulnerability because it grants attackers the ability to run any code of their choosing on the vulnerable system, effectively taking control of it.
In this context, ipping.php is likely intended to manage ping operations for network diagnostics. However, due to the lack of input validation, it can be manipulated to execute system commands beyond its intended scope.
Remediation
Official fix: Contact China Telecom for the patch that addresses the input validation flaws in the ipping.php script. This patch will sanitize inputs to ensure that malicious commands cannot be injected and executed.
Implementing the Fix
Upgrade your IPS signature database to version 3.0.208 and your AV signature database to version 2.1.558 to ensure that Hillstone Networks Next-Generation Firewall (NGFW), Hillstone Networks Intrusion Prevention System (NIPS), and Hillstone Breach Detection System (BDS) are equipped to detect and provide protection against this vulnerability.