Introduction
In the ever-evolving landscape of cybersecurity threats, a new variant of ransomware has emerged, which predominantly targets victims in South Korea. Known as BlackBit, this ransomware bears a striking resemblance to the notorious LokiLocker, albeit with a few cosmetic changes. Operating under the Ransomware-as-a-Service (RaaS) model, BlackBit showcases its capabilities to establish persistence, evade defense, and impair recovery.
Vulnerability
BlackBit is a 32-bit executable built using the .NET compiler and safeguarded by .NET Reactor that performs various actions upon execution. It starts by examining the keyboard layout of the target system. After targeting a host for infection, BlackBit copies itself to specific directories, such as “C:\ProgramData\”, and names itself “winlogon.EXE” to ensure persistence. Moreover, BlackBit replicates itself in the “C:\Users<user>\AppData\Roaming” and creates a task schedule, enabling automatic execution each time the user logs in.
To maximize its impact, BlackBit employs multithreading to execute a single command that eliminates shadow copies and system backups, and disables the system’s recovery. Before initiating the encryption process, it disables key security measures such as Windows Defender, the firewall, and the task manager. Additionally, BlackBit terminates multiple processes and halts specific services, ensuring the successful encryption of the victim’s files. During encryption, it modifies the filenames to a format like “[RickyMonkey@onionmail.org][Unique System ID]Actual-FileName.BlackBit”, while also generating a ransom note named “Restore-My-Files.txt”.
Remediation
Employ strict access control measures:
Implement multi-factor authentication (MFA) to enhance the security of critical systems and sensitive information. Strong password policies should be enforced to mitigate the risk of unauthorized access. Role-based access control (RBAC) ensures that users only have access to the resources required for their designated roles.
Implementing the Fix
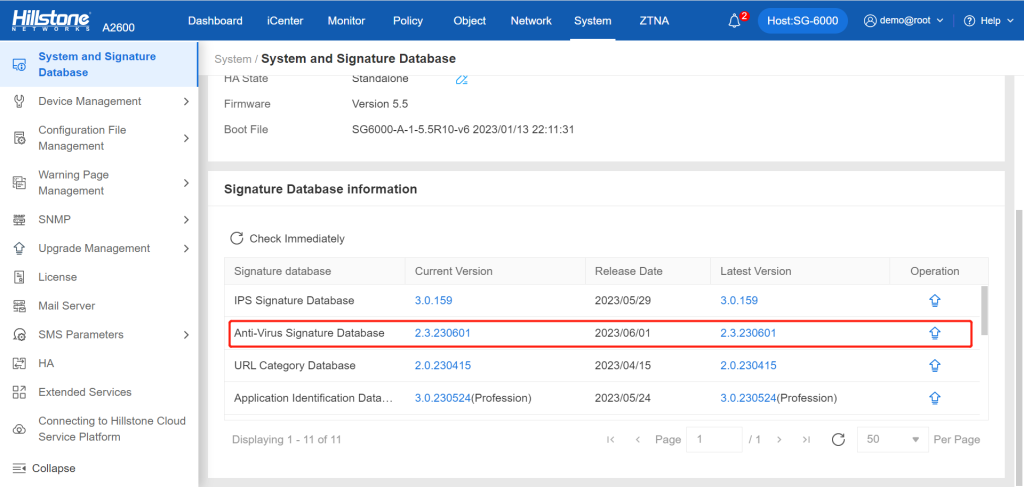
Hillstone is equipped to detect this vulnerability and furnish robust protection through its anti-virus prevention signature database (2.3.230531 and later). Products such as Hillstone NGFW, Hillstone CloudEdge, Hillstone Breach Detection System (BDS)and Hillstone Network Intrusion Prevention System (NIPS) can automatically activate and deploy this ability based on the signature database.