Introduction
MaaS (Malware as a Service) is a new mode of cybercrime where criminals sell or rent out malware on online platforms to make a quick buck. Recently, researchers stumbled upon a new MaaS platform called Cinoshi that offers various services like stealer, botnet, and crypto-miner. What’s even weirder is that, some of these services are entirely free!
This means attackers no longer need technical skills or resources to launch cyber-attacks. They can simply download and use malicious software from these platforms, causing havoc on a larger scale for organizations and individuals alike.
Vulnerability
The answer is revealed: Cinoshi Stealer is available for free and includes a panel that supports the build’s integration. According to its developers, the Stealer is capable of gathering information and capturing screenshots of the victim’s computer, extracting data such as passwords, cookies, and cards from over 35 encrypted wallets and browser extensions that are based on Gecko, Chromium, and Edge. The free service generates a stealer payload without any obfuscation or encryption, while an encrypted build can be obtained by remunerating 300 Rubles.
The payload is a 32-bit .Net binary file that utilizes various anti-tampering techniques, including heavy obfuscation and empty methods. It uses automatic de-obfuscation tools to modify its code during runtime, making it very challenging to obtain readable code.
Upon execution, the Stealer payload dispatches a request to hxxps[:]/tryno[.]ru/robots and uses ‘WebClient.DownloadString’ to retrieve the base-64 encoded content hosted on the site. Subsequently, the content is decoded, revealing the C2 URL hxxps[:]//anaida.evisyn[.]lol. The Stealer then proceeds to retrieve .NET dependency files from the C2 URL and stores them in the Stealer’s assembly location with hidden attributes.
Thereafter, the Stealer initializes multiple threads to carry out malicious actions. It initializes the paths to the directories that contain sensitive information for various applications and verifies their presence on the victim’s system using the Directory.Exists() method. Rather than creating physical files to store the pilfered data, this Stealer employs a MemoryStream. Finally, it generates a zip file and adds all the collected data to it for data exfiltration.
Remediation
Here are some crucial cybersecurity best practices that can establish the primary defense against attackers. Please consider implementing the following practices:
- Refrain from downloading pirated software from untrustworthy websites.
- Use strong passwords and enforce multi-factor authentication wherever possible.
- Ensure that automatic software updates are turned on for all connected devices.
- Use reputable antivirus and internet security software on all devices.
- Verify the authenticity of links and email attachments before opening them to avoid falling prey to phishing attacks.
- Monitor the network for data exfiltration and block suspicious URLs such as Torrent and Warez.
- Implement Data Loss Prevention (DLP) solutions on all systems.
Implementing the Fix
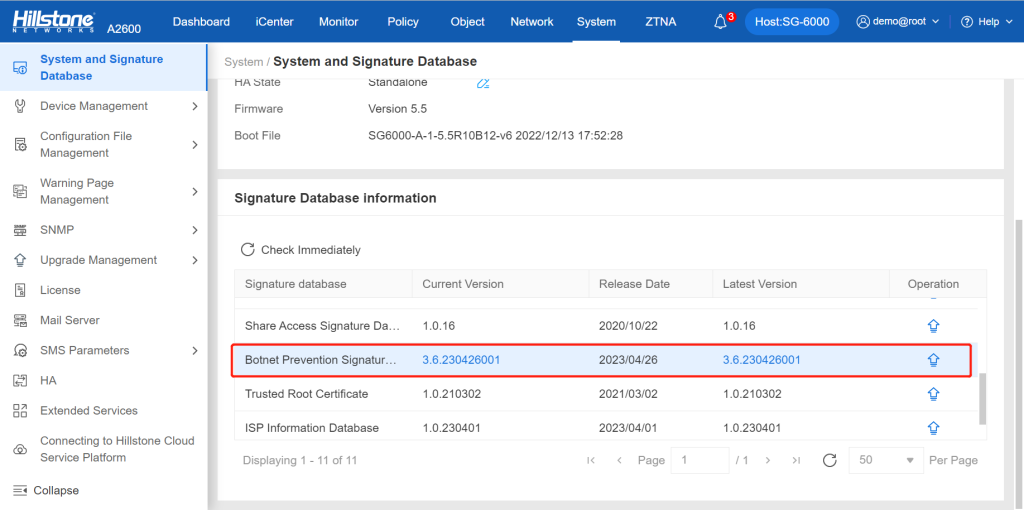
Hillstone is equipped to detect this vulnerability and furnish robust protection through its botnet prevention signature database (version 3.6.230426001 and higher). Devices such as Hillstone A-Series NGFW, Breach Detection System (BDS) and Next-generation Intrusion Prevention System (NIPS) can automatically activate and deploy this ability based on the signature database.