Introduction
VMware ESXi is a popular virtualization hypervisor worldwide. Recently, ESXi servers that are unpatched against a two-year-old remote code execution vulnerability – Open Service Location Protocol (OpenSLP) vulnerability (CVE-2021-21974) – have come under massive ransomware attacks.
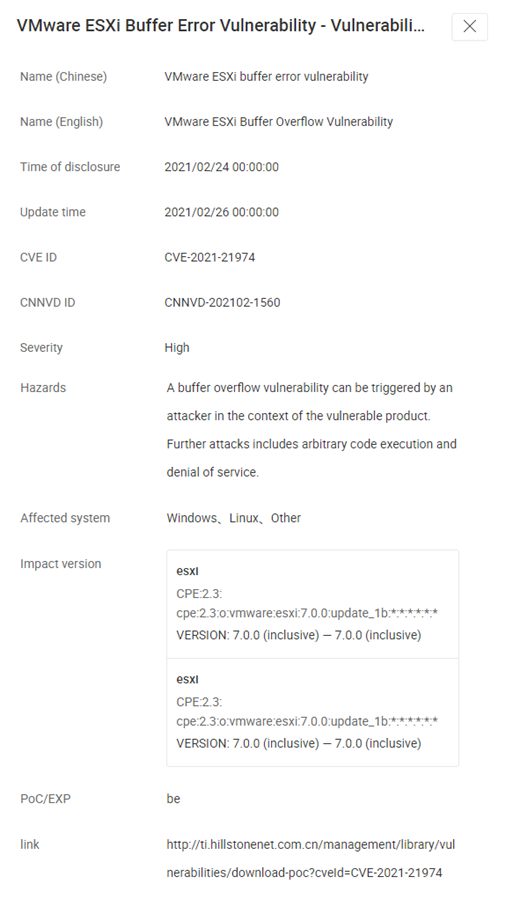
Vulnerability
The ransomware attacks exploit CVE-2021-21974 as a compromission vector, which is a heap-overflow vulnerability in the OpenSLP service. The attacker likely identifies hosts with OpenSLP vulnerabilities through scanning. Then, being within the same network segment as the target servers, the attacker is able to access port 427, trigger the heap-overflow issue, and execute code remotely, so as to deploy a new ESXiArgs ransomware.
The attacker creates files in the breached servers: encrypt (the encryptor ELF executable), encrypt.sh (a shell script that performs various tasks before executing the encryptor), public.pem (a public RSA key used to encrypt the key that encrypts a file), motd (the ransom note in text form), and index.html (the ransom note in HTML form). After the encryptor is executed, all the files with the .vmxf, .vmx, .vmdk, .vmsd, and .nvram extensions on compromised ESXi servers will be encrypted.
Affected Version
7.0 before ESXi70U1c-17325551
6.7 before ESXi670-202102401-SG
6.5 before ESXi650-202102101-SG
Remediation
1. Official fix: VMware has released the patches, and we recommend that users upgrade to the latest version.
2. Workarounds: Mitigate this risk by disabling the SLP service on VMware ESXi. Please visit:
https://kb.vmware.com/s/article/76372
Implementing the Fix
Hillstone Networks has collected intelligence on vulnerability CVE-2021-21974.
Hillstone Networks has updated the IPS signature database to defend against vulnerability CVE-2021-21974. Based on this, the Hillstone Networks Next Generation Firewall (NGFW), Hillstone Networks Intrusion Prevention System (IPS) , and Hillstone Server Breach Detection System (sBDS) can support the detection and protection of this vulnerability.
Moreover, sBDS can support the detection and protection of ransomware attacks.
The Hillstone Networks iSource can assist in response to threat events caused by this vulnerability in partnership with sBDS.



