Nearly 300 new features and enhancements
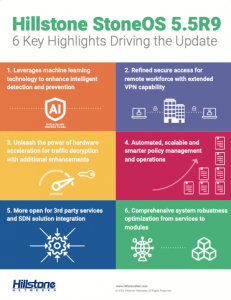
Hillstone StoneOS 5.5R9
Read about the six highlights that were updated in StoneOS 5.5R9 below.
Leverage machine learning technology to enhance intelligent detection and prevention
Cyberattacks now leverage advanced techniques to transport exploits or attacks, which continue to challenge the security teams of organizations. The latest StoneOS update continues to enhance the intelligent detection and prevention capability on the next generation firewalls. The new machine learning based algorithms for detecting DGA help improve the accuracy and effectiveness of detection to keep organizations on top of unknown threats. The extended support of a cloud sandbox also allows for more unknown threat detection, and intelligence sharing across Hillstone NGFW families including data center firewalls.
Enhanced unknown threat detection through:
ML powered DGA detection:
DGA—domain generation algorithms—on infected hosts generate pseudo domain names randomly, including C&C server domain names. The latest StoneOS release leverages the machine learning capability to train the new detection model with the latest DGA data set. It also introduces additional features to be extracted from the domain name for modeling. Besides, it allows live updates of the detection model in the form of signature database.
New platform and new file types supported on Cloud sandbox:
Hillstone’s cloud sandbox leverages machine learning technology to detect malicious files. It is now available for the X series data center firewalls. This means chassis-based, high-performance appliances can now send malicious files to the cloud sandbox for unknown threat detection. The new release also supports ELF file and scripts on Cloud sandbox, which extends the malicious file detection to Linux based hosts in addition to Microsoft Windows hosts.

Refined secure access for remote workforce with extended VPN capability
As digital transformation continues and the remote workforce transitions from a fad to a reality, organizations are looking for feature rich VPN solutions which not only ensure secure remote access or site-to-site connection, but solutions that can meet the growing demand at a lower TCO. The new StoneOS release brings additional VPN features that support extended user scenarios, a configuration wizard that help improve the user experience, and a performance upgrade to address the increasing traffic from remote workforces.
All-encompassing VPN features such as:
L2TP client support:
This allows the firewalls in the branches to establish a tunnel to the headquarter over L2TP, which provide cost-effective access to the headquarters for the branches and its remote access users.
IPsec VPN configuration wizard:
IPsec VPN are frequently used but can include long and complicated configurations. With the new IPsec VPN configuration wizard on WebUI, you can search for phase 1 or phase 2 proposals during configuration, or copy peer name or IPsec VPN to initiate a similar configuration. This helps increase attention to detail, eliminates accidental errors, and improve efficiency.
IPsec VPN acceleration:
The new release takes full advantage of the hardware acceleration capability to optimize the performance of IPsec VPN. It provides customers a cost-effective solution to handle the increasing traffic from remote workforces.
And more…

Unleash the power of hardware acceleration for traffic decryption with additional enhancements
SSL proxy is now quite popular in modern web application deployments as it can provide extra security and anonymity. The new StoneOS release optimizes the throughput performance and introduce the whitelist capability, which helps cover some scenarios where certain addresses or domains should be exempted.
Hardware acceleration result in augmented features, such as:
Performance improvement of SSL proxy with HW acceleration:
The new release takes full advantage of the hardware acceleration capability to optimize the performance of SSL proxy, which significantly improved the SSL proxy throughput.
SSL proxy support whitelist:
Some web applications or services are not appropriate for proxying due to either business concerns such as privacy, or technical reasons such as client certificate authentication or SSL pinning. This feature enables those domains in the whitelist to be exempted for proxy.
Automated, scalable and smarter policy management and operations
The complexity of policy management increases as an organization expands and business grows. The new mini policy feature simplifies the configuration by allowing central orchestration systems to quickly add or delete up to 1 million mini policy entries to meet the dynamically changing security requirements. Additionally, the automation of policy operations, including the app-based policy (rule) generation and NAT policy redundancy check, brings high efficiency.
Policy creation and configuration process is streamlined through:
Millions of mini policies:
Mini policy entry contains 5-tuple, source and destination zone, and an ALLOW or DENY action. Via north bound REST API, the integrated orchestration system can quickly add or delete up to one million mini policy entries to meet fast-changing security requirements from the field. The design of mini policies ensures consistent policy enforcement on all FW security features with extreme scalability.
App based policy (rule) generation in policy assistant:
With this function, traffic will be analyzed and policies can be generated based on the applications. It makes the policy configuration easier to create and friendlier to read, which helps reduces the complexity and minimize potential configuration errors.
Support auditing of policy configuration:
This feature brings meta data such as config version and reason description into the workflow, enabling the lifecycle management of policies and provides an interface for the auditing of policy configuration.
More open for 3rd party services and SDN solution integration
StoneOS becomes more open than before. In addition to RESTful APIs and SNMP, the new StoneOS supports configuration and management over Netconf. Beyond that, the system also fully leverages external services and resources that eventually help improve the threat detection and simplify the daily operation.
StoneOS is more integrable through features such as:
Support management over Netconf:
Netconf is now popular in software defined network (SDN) based infrastructure as a network management protocol. The latest StoneOS now support configuration and management over Netconf by 3rd party SDN controller.
Import PTF blacklist from external dynamic lists:
In addition to the traditional manual configuration, the IP black list of perimeter traffic filtering could be adjusted dynamically by importing members from external files or external feeds over HTTPS or FTP, thereby potentially avoiding a huge amount of repetitive work for manual configuration.
Comprehensive system robustness optimization from services to modules
Continuity of service without failures or interruptions is the ultimate experience that Hillstone would like to bring to the end users. Beyond extending high availability solutions to IPv6, the new StoneOS release also brings service level robustness by redesigning the software architecture and module level optimization for the data center firewalls.
StoneOS bolsters business continuity with:
Millions of mini policies:
Hotfix support on NFGW:
By re-designing the software architecture, the latest StoneOS now supports fixing an issue on a live NGFW without creating a system downtime or outage. More than that, you may also restart services like PPPOE or SYSLOG without rebooting the system.
IPv6 support on HA peer mode:
HA peer mode provides the active-active high availability solution even in asymmetric routing deployment scenario. This capability now has extended to IPv6 environment.
SCM failover when in high memory usage on X series firewall:
The active security control module (SCM) on the X series chassis-based firewall now monitors its memory usage and switches to the passive SCM when it is out of memory. This avoids an unnecessary system reboot caused by losing the keepalive heartbeat of SCM in that special case, ensuring undisrupted business continuity.
Offline upgrade of application signature database:
Customers who deployed their devices with poor Internet connection or with limited access to upgrade servers can now upgrade application signature databases by downloading the upgrade package file from Hillstone’s upgrade service portal.
Hillstone StoneOS Resources
Expanded Protection with a Future-proof Technology and an Intuitive User Experience
With about 300 new features and enhancements, the latest Hillstone StoneOS 5.5R9 empowers organizations with an intelligent, reliable and automated security solution. These advanced features help users stay ahead of known and unknown threats, attain an elevated decryption and encryption performance out of the hardware acceleration, automate policies for improved visibility, and improve the system robustness and availability with a broader 3rd-party integration capability. All these enhancements and new features enable customers to adapt to the fast-changing threat landscape as well as the infrastructure’s constant evolution.
Download the 2021 Gartner® Magic Quadrant™ for Network Firewalls

Learn More about Hillstone’s Product Portfolio
Engage with us to learn more about Hillstone’s solutions by contacting your local authorized Hillstone Networks reseller.
Contact Us
Disclaimer:
Gartner, Magic Quadrant for Network Firewalls, 1 November 2021, By Rajpreet Kaur, Jeremy D’Hoinne Et Al
GARTNER and Magic Quadrant are registered trademarks and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Hillstone Networks.
Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.