The threat environment is constantly evolving; both attack types and volumes increase dramatically each year. As a result, security breaches are increasing accordingly.
After each security breach, organizations ask, “How did the attacker get in? How are they getting around?” and other similar questions. They want more visibility into the attack techniques used in the breaches, and to understand how to fix the gaps that exist in their security infrastructure.
The MITRE ATT&CK framework is designed to help answer these questions by providing a common way to describe attack techniques and their mitigations. Organizations can leverage the MITRE ATT&CK framework to identify holes in defenses, and prioritize the fixes based on risk.
About the MITRE ATT&CK Framework
The MITRE ATT&CK framework is a knowledge base of attack behaviors and taxonomies that provides comprehensive coverage of attack behaviors in the wild. The framework is open and available to any person or organization for use at no charge; therefore, the framework brings large communities together to develop more effective cybersecurity. Most security providers integrate the MITRE ATT&CK framework into their products, ranging from SIEMs, endpoint detection and response, and sandboxes to network defense.
The ATT&CK matrix for enterprises classifies attack behaviors into 14 primary categories:
- Reconnaissance
- Resource Development
- Initial Access
- Execution
- Persistence
- Privilege Escalation
- Defense Evasion
- Credential Access
- Discovery
- Lateral Movement
- Collection
- Command and Control
- Exfiltration
- Impact
Each category lists multiple defensive and mitigation techniques, and most of them include sub-techniques. By mapping the threats seen in their network against the ATT&CK framework, admins can confidently tune their solutions and defend against these threats to mitigate their impact.
Using the MITRE ATT&CK Framework with a Sandbox
For security sandbox products, it is quite common to integrate the MITRE ATT&CK framework. In a nutshell, the sandbox provides virtual and constrained environments for malware to play out their attacks. In ideal scenarios, the sandbox will capture attack techniques throughout the attack lifecycle.
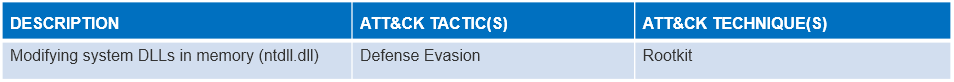
The MITRE ATT&CK framework helps sandbox users better understand the attack behaviors of malware and the specific techniques that adversaries may use in conjunction with others. For example, a sandbox may capture a behavior that writes the memory where ntdll.dll is located. The sandbox describes this behavior as “Modifying system DLLs in memory (ntdll.dll).”
However, this nomenclature may not be very straightforward to understand. After mapping into the MITRE ATT&CK tactics and techniques, the behavior is described as “Defense Evasion” and “Rootkit” by the standardized classification in MITRE ATT&CK’s knowledge base. Through this mapping, the behavior becomes much easier to understand.
In the ATT&CK database, you can then scroll down under the Defense Evasion column to the Rootkit technique. Clicking on this link gives you a list of threats that use this technique, their mitigations and detection options.
A Second Example: Software Packing
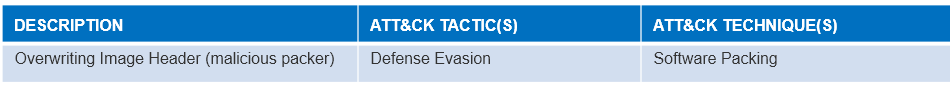
Let’s look at another example. A sandbox finds that a malware tries to overwrite an existing PE file image in memory. The sandbox describes this behavior as “Overwriting Image Header (malicious packer).” However, this may not be very straightforward to understand.
After mapping this behavior into MITRE ATT&CK tactics and techniques, the behavior is described as “Defense Evasion,” with a technique of “Obfuscated Files or Information,” and a sub-technique of “Software Packing”. As before, the sub-technique page provides a great deal of information on examples of threats, their mitigation, and detection techniques.
As these examples show, the MITRE ATT&CK framework helps administrators turn sandbox logs into actionable tactics to defend against attacking behaviors of malware.
The Hillstone Server Breach Detection System (sBDS), Network Intrusion Prevention System (NIPS), and Next Generation Firewalls (like the Hillstone A-Series, E-Series, and X-Series datacenter NGFW) all include Cloud Sandbox capability. Hillstone’s Cloud Sandbox is an advanced threat detection platform that can emulate the execution environment and analyze all activities related to malicious files, identify advanced threats and then collaborate with sBDS, NIPS and NGFW solutions to provide rapid remediation.
To learn more about the MITRE ATT&CK framework, view the official publication. If you need assistance or would like to discuss how Hillstone and ATT&CK can help your organization, please reach out to us.



